Hackers and hacker groups are always trying to outdo each other and always trying to grab attention, so everything they say should be taken with a grain of salt.
That said, there have been so many breaches at so many places with hilariously bad security practices that there's not much that will surprise us as this point.
With that, AnonymousIRC just unloaded one million and one iPhone and iPad UDIDs, that is Unique Device Identifiers which are exactly what they sound like, a unique id assigned to each device to make it easier to track, essentially.
The group, or whoever is behind the Twitter username, posted the leak as part of the AntiSec movement and said it's in possession of 12 million such IDs along with the personal information of the people who own the devices with said IDs.
The group claims to have gotten its hands on the data from an FBI laptop which got hacked. On it, sat a single CSV file conspicuously titled "NCFTA_iOS_devices_intel.csv" and containing personal data on the owners of more than 12 million Apple devices 12,367,232 devices to be exact. NCFTA would stand for National Cyber-Forensics & Training Alliance.
The data turned out to contain the UDID, user name, device name, type of device, Apple Push Notifications Service Tokens, zipcode, cellphone number, address and all other personal info regarding the owners of the devices.
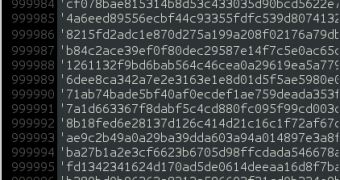
The Anonymous group decided to release data on 1,000,001 devices, a nice round number. It only released the UDIDs, the push notifications tokens, the device's name and the device type. It should be enough to verify the data and determine whether it is legitimate.
The decrypted file does contain one million and one records of what appear to be legitimate UDIDs along with device names, device types and the push notifications tokens.
The leak was announced on pastebin, as is the tradition, with the actual text file posted on various filesharing sites. You'll find instructions on where to find it and how to decrypt it in the announcement, but you do it at your own risk.
 14 DAY TRIAL //
14 DAY TRIAL //