Experts from ESET and Russian firm Group-IB have been closely monitoring the activities of Carberp botnets and their masters and they're proud to state that all the cybercriminals involved in these operations have been arrested.
As expected, the number of infected devices dropped right after each series of arrests, but for the time being, the number of impacted computers is still high.
Carberp first came to light in 2009 when a group started using it to steal sensitive information. At the time, the malware wasn’t as sophisticated as the more recent variants, mainly relying on legitimate remote access software.
In 2010, a second organization began its activities and in the summer of 2011, the biggest botnet based on Carberp was born. A few months later, the Trojan was improved to incorporate even a bootkit.
By the end of 2011, things were really getting out of hand, mass infections being served from hijacked websites.
Each of these versions came with new features and improved mechanisms such as a smartcard detection functionality.
Fortunately, starting with March 2012, law enforcement agencies managed to apprehend the individuals that coordinated the massive operations. At the end of June, a man suspected of running the largest banking botnet in the world (4.5 million computers) was arrested.
The figures provided by ESET's Live Grid show that after each series of arrests, the number of detections slightly dropped, but the number of infected machines is still high, compared to the past years.
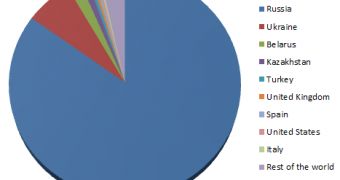
“All the Carberp botnet organizers have been arrested, but our statistics aren’t showing a big drop in detections. The Russian region leads as before for Carberp detections and after the arrests it showed a brief dip,” said Aleksandr Matrosov of ESET’s Security Intelligence Team Lead.
The fact that a cybercriminal responsible for a massive botnet was arrested is good news, but it will remain to be seen if the infection rates will be considerably influenced by this “unique case,” as researchers call it.
 14 DAY TRIAL //
14 DAY TRIAL //